With summer vacations taking employees out of the office, phishing attacks are on the rise. Here are three ways companies...more


With summer vacations taking employees out of the office, phishing attacks are on the rise. Here are three ways companies...more
Cisco commissioned Forrester Consulting to conduct a Total Economic Impact™ (TEI) study and examine the potential return on investment (ROI)...more
The digital transformation era is changing how organizations leverage technology to fulfill their business objectives. One key change is in...more
Organizations often struggle to achieve an effective security posture because of the complexity of managing disparate point security solutions that...more
Network firewalls are a critical line of defense in securing enterprise networks and protecting their vital data. The rapid transition...more
Businesses today are more than standalone organizations. They have complicated ecosystems with intersections between the corporation and their customers, suppliers,...more
Maintaining strong network security has become more challenging than ever in today’s educational ecosystem. That’s because the adoption of advanced...more

Image: Konstantin Savusia/Adobe Stock For app developers, Low-Level Virtual Machine bitcode has been a staple of Apple’s toolchain and the...more
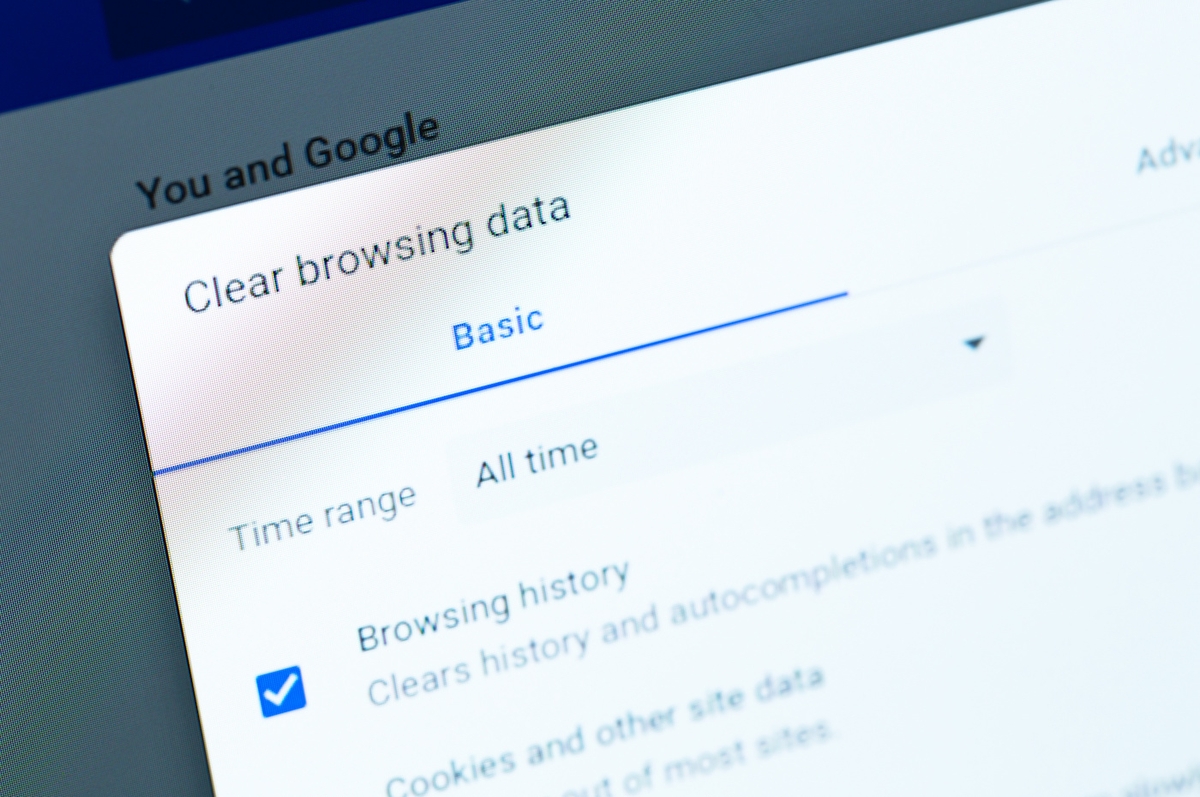
The search giant explained that it pushed back its timeline once again because it needs more time for testing to...more

Save money and save your information from falling into the wrong hands with the InsecureWeb Dark Web Monitoring platform. Image:...more