The company found that Google-related URLs were the most frequently abused last year. Image: xijian / Getty Images As part...more


The company found that Google-related URLs were the most frequently abused last year. Image: xijian / Getty Images As part...more

Image: Adobe Must-read security coverage A 2022 report on privileged user threats by Ponemon Institutes suggests that privileged user attacks...more

The number of cybersecurity protection tools on the market is staggering, which makes it challenging to decide which to use....more
A new banking Trojan dubbed "Malibot" pretends to be a cryptomining application to spread between Android phones. While only active...more

[video src="https://d1rytvr7gmk1sx.cloudfront.net/wp-content/uploads/2018/08/20180810-VPN-Brandon.mp4" poster="https://d1rytvr7gmk1sx.cloudfront.net/wp-content/uploads/2018/08/20180810-VPN-Brandon.mp4"]Virtual private networks have risen from obscurity to become the frequently preferred method of linking private networks. Although...more

In this step-by-step guide, learn how to enable the backup feature within the two-factor authentication application Authy. Image: madedee/Adobe Stock...more

Image: yurich84/Adobe Stock The Dark Web is a small portion of the Internet, but it concentrates many cybercriminals and threat...more

Image: Sashkin/Adobe Stock Websites crash for numerous reasons, but you can boil it down to one thing: Dependence. For us,...more
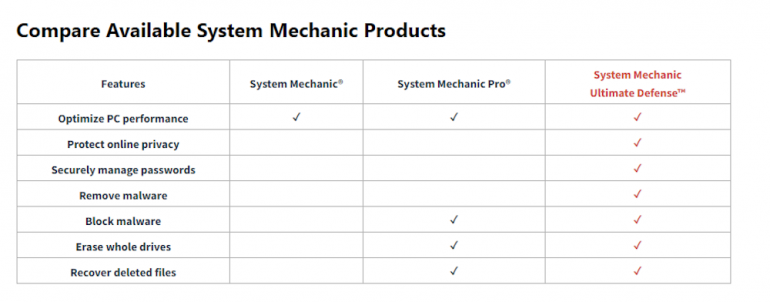
I’m a huge proponent of Swiss Army Knife-type products that can perform multiple useful functions to help keep systems running...more

Proofpoint says the piece of functionality allows ransomware to encrypt files stored on Microsoft SharePoint and OneDrive. Image: Adobe Stock...more