A recent survey reveals many organizations close either temporarily or permanently after a ransomware attack. Learn more about how you...more


A recent survey reveals many organizations close either temporarily or permanently after a ransomware attack. Learn more about how you...more

Image: Prostock-studio/Adobe Stock The disruptions in the physical world have spilled over, creating “digital ripples” that require us to care...more

When it comes to securing their organizations, CISOs need to focus on the human in the loop. Image: A Stefanovska/Adobe...more

Malicious traffic might be running rampant on your network. Jack Wallen shows you how to deploy a simple monitoring system...more

Apple announced iOS 16 on June 6, 2022 during the WWDC keynote. Image: Apple During Apple’s WWDC keynote on June...more
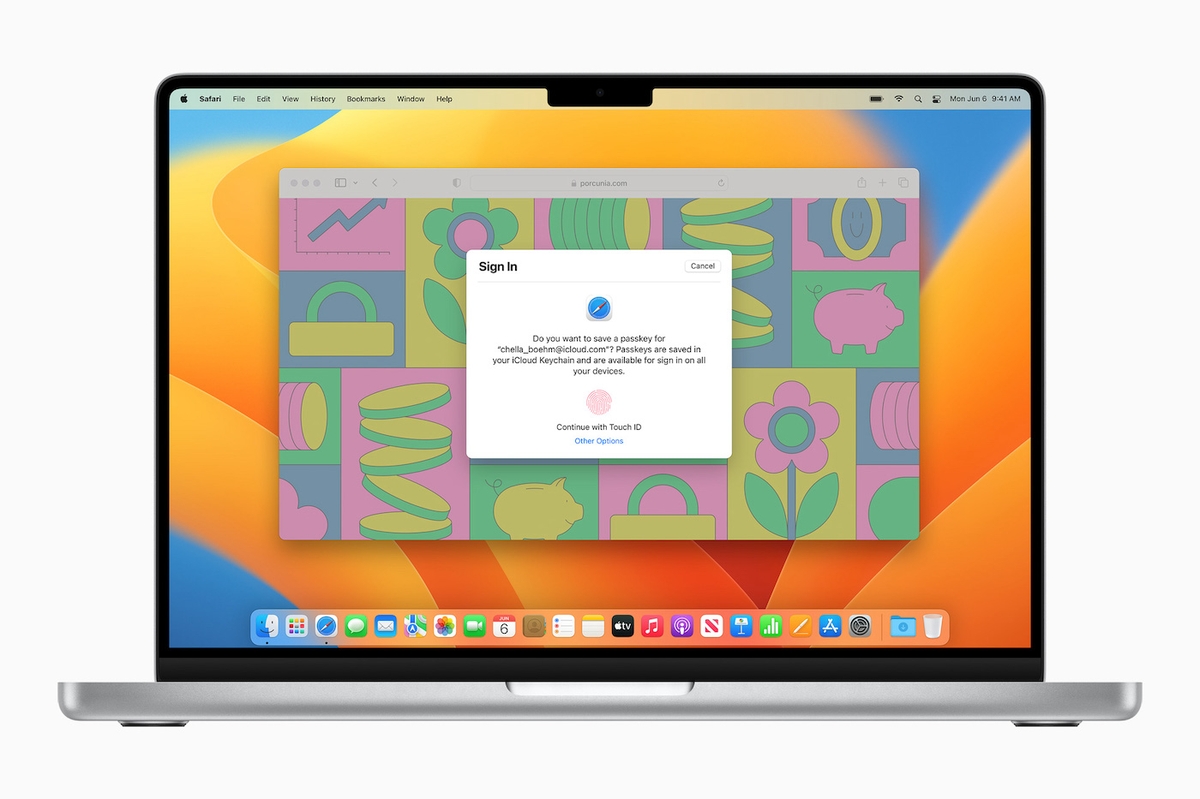
Passkeys use cryptographic techniques and biometrics and aim to replace passwords for good. Image: Apple During its WWDC, Apple introduced...more

Check out these features from Authy and Google Authenticator before deciding which authentication tool is best for you. Image: Getty...more

WordPress has many managed hosting plans to choose from to help handle larger websites with higher traffic flows. Determine whether...more

The internet-facing instances are currently being accessed by attackers who remove the vulnerable databases and leave a ransom note instead....more

Dell storage customers interviewed are achieving a 60% savings over six years when they use Technology Rotation for their storage...more