Recruiting a Security Analyst with the right combination of technical expertise and experience will require a comprehensive screening process. This...more
Security

Protect your environment with deception and honeytokens
Image: Adobe Stock You can’t afford to be reactive with security any more. Instead of waiting until you notice an...more

AnyDesk vs TeamViewer: Remote desktop software comparison
When it comes to remote desktop software, AnyDesk and TeamViewer are two top contenders. Which one is the best choice...more

Why you need secured-core Windows servers
Image: Production Perig/Shutterstock Microsoft has been focusing on hardware-based security recently, with Windows 11 requiring use of TPMs and other...more
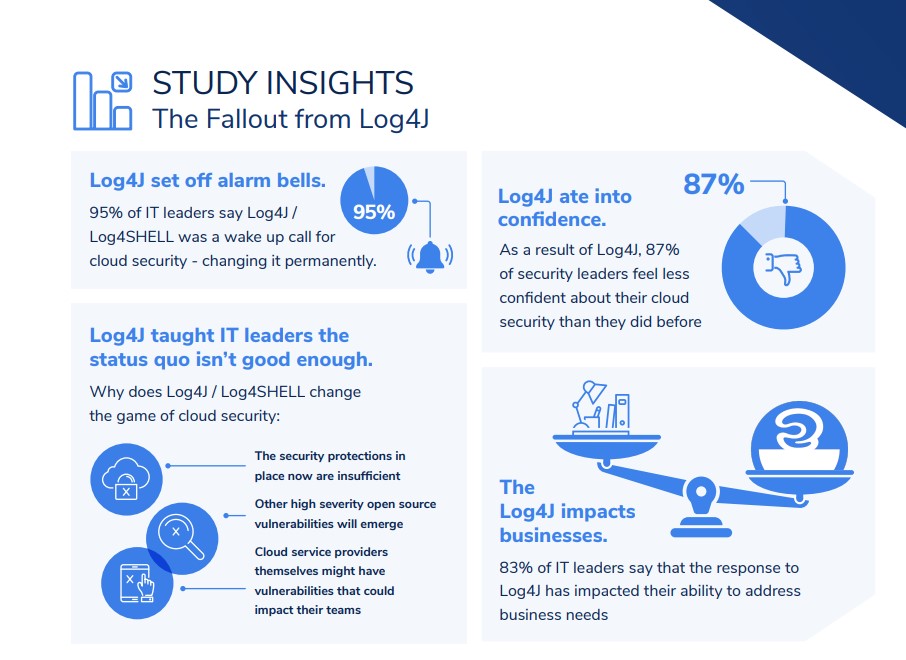
Survey: Recovery from Log4Shell vulnerability is ongoing with 77% of organizations still in patching mode
New research shows that the weakness shattered confidence in cloud defenses and motivated a new set of cybersecurity priorities. Image:...more

Best advanced threat protection tools and solutions 2022
Image: iStock/weerapatkiatdumrong Just as malicious actors refined virus, phishing and ransomware attack practices and technologies, so have cybersecurity providers improved...more

IAM software: Okta vs Azure Active Directory
Okta and Microsoft Azure Active Directory are both robust and capable IAM solutions. Okta wins out on ease of use...more
Safeguard Your Infrastructure from Ransomware and Cyber Threats
Cyber attacks will continue to be a threat to businesses, but with Dell Technologies you can have peace of mind...more

OneLogin vs Okta: Comparing IAM solutions
Which identity and access management software should you choose? Compare the features of OneLogin and Okta to see if either...more
Okta vs Ping: IAM software comparison
This review compares the features of IAM software Okta and Ping. Features include multifactor authentication, threat detection and dashboards. Image:...more