What is the best way to deliver business continuity in today’s rapidly changing environment? You need agile deployments that seamlessly...more
Security
Advanced Threat Defense for Your Business-critical Applications on AWS
Fortinet’s partnership with AWS ensures your workloads and applications on AWS are protected by best-in-class security solutions. With simplified security...more
Best Practices for Managing the 3 Levels of AWS Security
The nature of the expanding attack surface and advanced threats necessitates broader, more comprehensive protection. Therefore, security architects tasked with...more
The Key to Optimizing Cloud Security on AWS eBook
Join or sign in Register for your free TechRepublic membership or if you are already a member, sign in using...more
Autodesk Leverages Adaptive Cloud Security
Autodesk needed scalable and secure cloud security to build new applications and extend internal data centers. Fortinet’s Adaptive Cloud Security...more
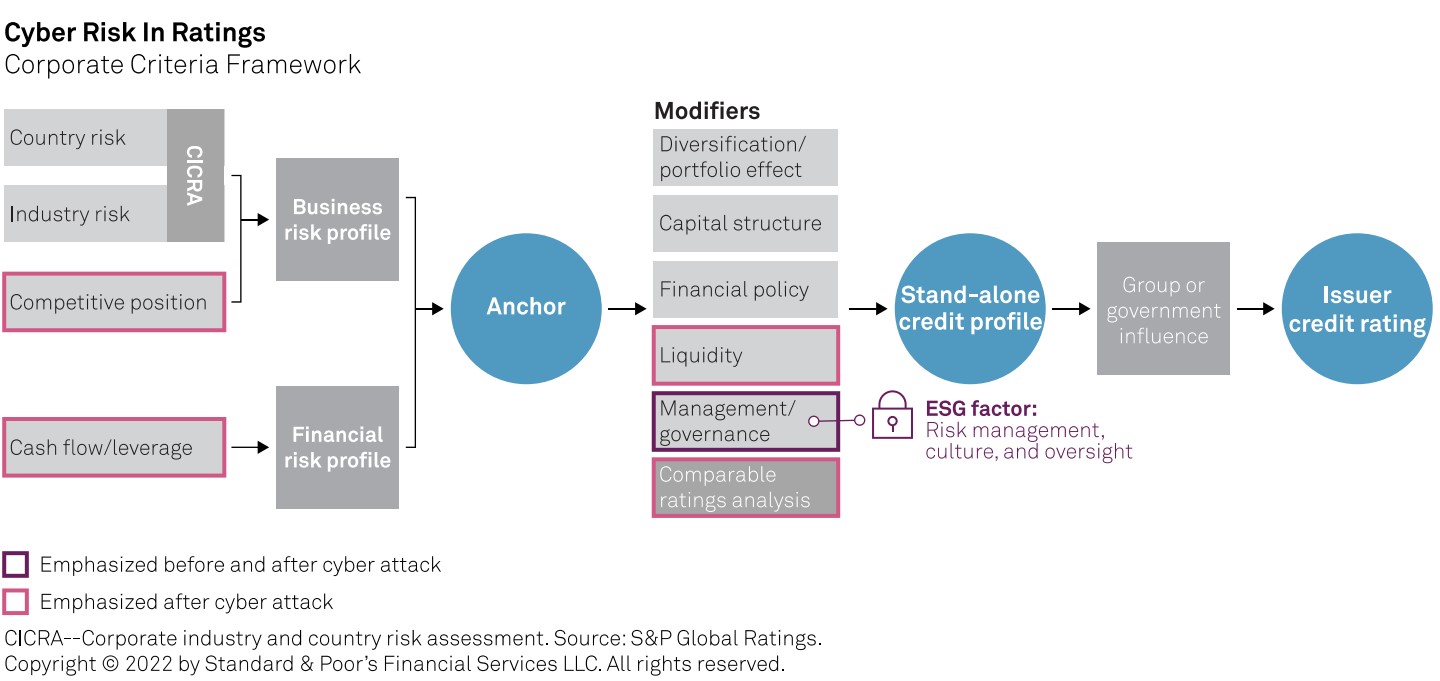
Credit agency warns weak cybersecurity defenses could hurt a company’s credit rating, even before an attack
S&P Global Credit adds cybersecurity to list of risk factors for evaluating credit scores and will use NIST standards for...more

Hackers employ voicemail phishing attacks on WhatsApp users
The scam was able to bypass Google and Microsoft’s email security filters after appearing to come from a legitimate email...more

Developers do not view application security as a top priority, study finds
Training may help alleviate some of these issues, along with clearer directives by management. Image: Sarah Pflug/Burst While most would...more
Weave Security Through Your SDLC from Idea to Maintenance
SafeStack Academy’s community-centric Secure Development training gives developers, testers, analysts, and architects the skills they need to build high-quality, secure...more
Software security roadmaps: Secure your software without the expense
Making your software more secure is a process that takes careful planning, a lot of collaboration, and a healthy dose...more