The two companies announced a joint agreement to work towards bettering the country’s infrastructure against cyber threats. Image: Andriy Onufriyenko...more


The two companies announced a joint agreement to work towards bettering the country’s infrastructure against cyber threats. Image: Andriy Onufriyenko...more

Single-cloud environments are said to be redundant. One expert disagrees and explains why. Image: iStockphoto/Denis Isakov Before cloud computing burst...more
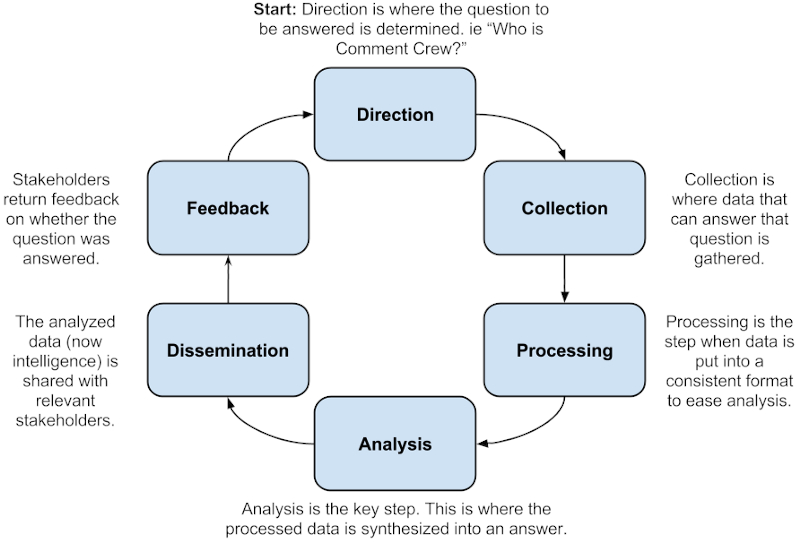
Cyber threat intelligence (CTI) is a concept that is crucial to the security of corporate networks, yet it can be...more
If you'd like a little more privacy when surfing the web, Firefox offers a few different options to defend yourself...more

A password generator can help when you need a strong and complex password to protect an account. Image: Getty Images/iStockphoto...more

Learn how to securely store notes along with your account credentials with iCloud Keychain and sync them to all of...more

Corporate users are more aware of phishing attacks in their mailboxes. Yet they are not used to being targeted via...more
To build an effective ICS cybersecurity strategy, it is crucial to identifythe security events that are most likely to occur....more
Giving employees the flexibility to be fully productive while working remotely makes it critical that businesses have endpoint security measures...more
When it comes to IT, disruption is just another day at the office. From fending off cyberattacks to incorporating leading-edge...more