A report from Claroty finds ransomware attacks against critical infrastructures rampant, and paying ransoms often results in less downtime and...more


A report from Claroty finds ransomware attacks against critical infrastructures rampant, and paying ransoms often results in less downtime and...more
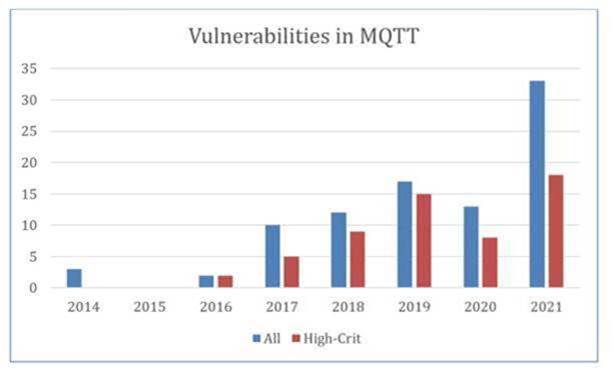
Security analysts found 33 weak points in MMQT, a frequently used protocol that rarely involves authentication or encryption.Kaspersky security researchers...more

[embedded content]You’ve probably heard some of the commonly circulated advisories for athletes traveling to the 2022 Winter Olympics in Beijing...more
APT group Armageddon was identified as acting against Ukraine late last year, and Symantec’s own data backs up that presented...more
Use the guidance in this report to learn more about the Ransomware-as-a-Service (RaaS) model and help protect your organisation from...more

Flashpoint and Risk Based Security’s report found that, despite early reports, the total number of breaches is likely much higher...more

Image: iStockphoto/Igor KutyaevWhat is an incident in the world of cybersecurity? NIST provides the following definition: “A computer security incident...more

The hacker that made off with millions from blockchain bridge service Wormhole exploited an incredibly common coding error that could...more
The XDR market is confusing, as is often the case with new security technologies Don’t wait to be proactive about...more