QR codes are everywhere, and they can also be dangerous. Here’s how to stay safe with some hints from Tom...more


QR codes are everywhere, and they can also be dangerous. Here’s how to stay safe with some hints from Tom...more

Phishing attempts are within reach of less tech-savvy attackers, thanks to the rise of phishing kits. Learn where these kits...more
The FCC has listed the Russian cybersecurity company and a pair of Chinese telecommunications businesses to its list of potential...more

Image: Microsoft Contents Encryption is the process of securing information by translating it into a sort of computer code that...more

Nutanix’s new report details why the move to multicloud is important for security. Image: Natali_Mis, Getty Images/iStockphoto Despite multicloud becoming...more
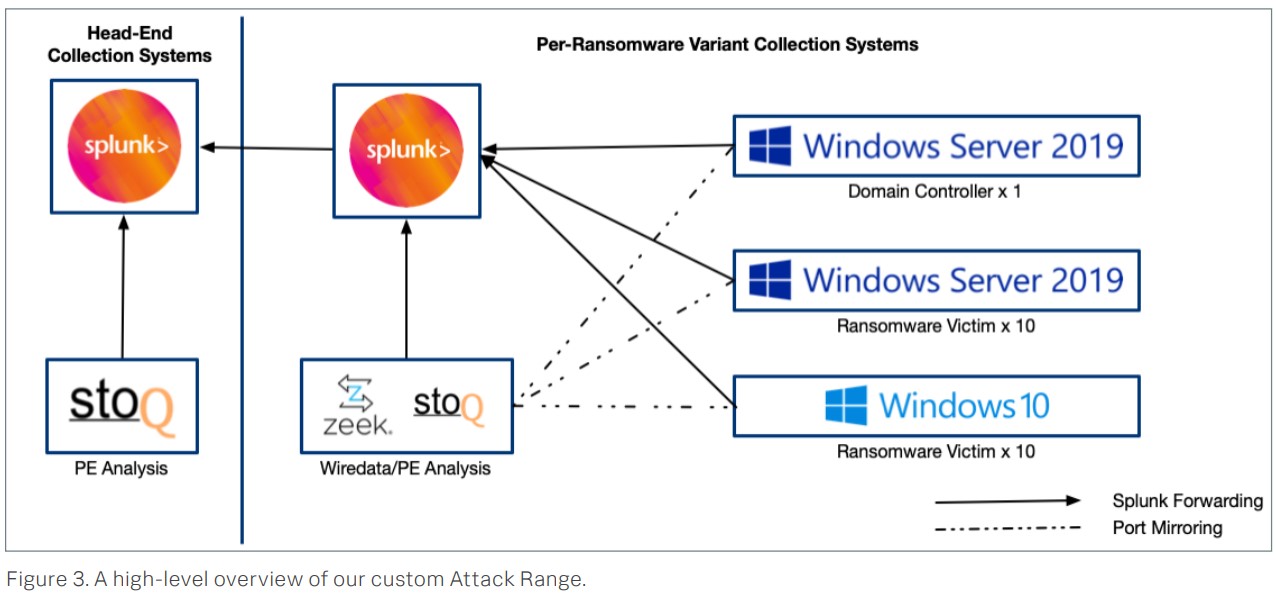
Security researchers tested 10 malware variants and found speeds ranging from four minutes to more than three hours to encrypt...more

Apple's iOS allows you to choose your own password manager. Learn how to make that change and integrate your passwords...more

In a world of escalating security threats, organizations need a solid platform to defend their critical assets. As you weigh...more

A new study from Kaspersky found that businesses’ biggest challenge when deploying IoT devices is making sure the solutions are...more

Image: Keeper Contents Apple’s macOS and iOS include a built-in password management system called Keychain Access, which is supplemented by...more