A credential harvesting campaign spotted by INKY at the end of February tried to lure its victims to Calendly, a...more


A credential harvesting campaign spotted by INKY at the end of February tried to lure its victims to Calendly, a...more

A phishing technique called Browser in the Browser (BITB) has emerged, and it’s already aiming at government entities, including Ukraine....more

Have you been considering a change of careers? Or would you just like to learn more about cybersecurity? Here's your...more

The two tech companies are believed to have provided hacker groups with user information as part of the impersonation. Image:...more
Image: Cisco Talos Quantum technology that the world’s superpowers are developing, if successful, will render many current encryption algorithms obsolete...more
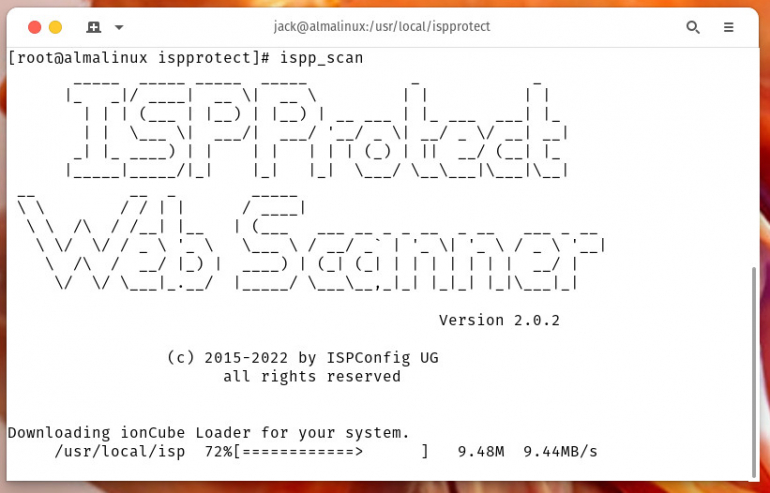
Websites should be scanned regularly for malware. Jack Wallen shows you how to do this on Linux with the help...more

A vulnerability affecting Google Chrome allows attackers to execute remote code on targeted users. Two North Korean threat actors are...more

Image: Adobe Stock Security of networks and systems is something every business and administrator should take very seriously. After all,...more

To reduce security threats within your organization, you must prioritize security risk management. Here are some best practices to follow,...more

Skip to content TechRepublic Premium Join / Sign In Account Information TechRepublic close modal Join or sign in Register for...more