From emailing vendors to communicating with team members, serious business happens in the inbox. That's why it's critical to secure...more


From emailing vendors to communicating with team members, serious business happens in the inbox. That's why it's critical to secure...more

Organizations are facing higher risks of cyberattack as criminals exploit unknown or unmanaged internet-facing assets, says JupiterOne. Image: iStockPhoto/1550539 IT...more
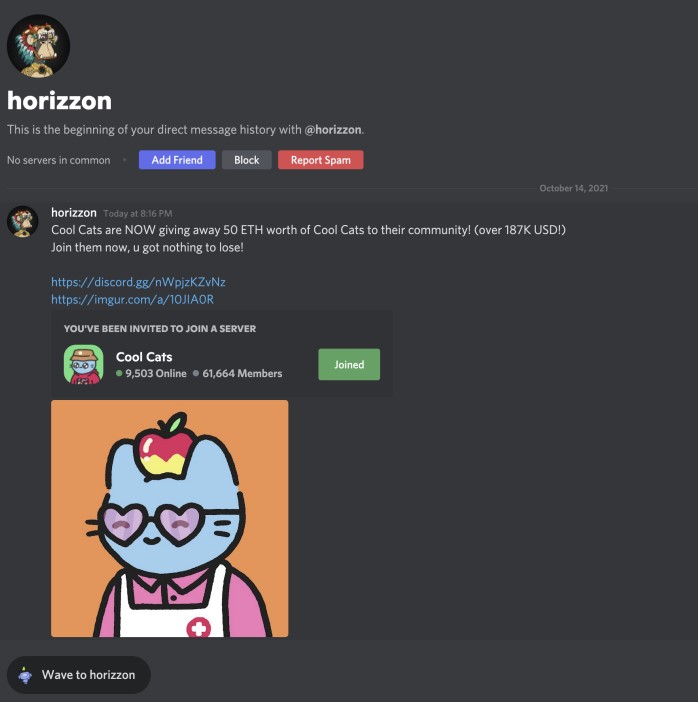
A Cisco Talos researcher explains how to spot malicious smart contracts, sleepminting and other pitfalls in the world of non-fungible...more

Half of the security pros surveyed by Laminar said their cloud environments were hit by a data breach in 2020...more

Veritas Technologies has released a study outlining the security issues with open source container orchestration system, Kubernetes. Image: Getty Images/iStockphoto/123dartist...more

The AvosLocker Ransomware as a Service (RaaS) group has targeted critical infrastructure sectors in the US, such as financial services,...more
Just because you use Linux, doesn't mean you shouldn't take security precautions. Jack Wallen shows you how to run a...more

Cybersecurity changes rapidly, but one thing remains constant. Threats don’t seem to slow down. If your network and security tools...more

The malware has been found in the French construction and government sectors and uses steganography, Tor proxy and package installer...more

Skip to content TechRepublic Premium Join / Sign In Account Information TechRepublic close modal Join or sign in Register for...more