Jack Wallen tests the Acronis Cyber Protect Home Office app, a disaster recovery tool anyone can use to create a...more


Jack Wallen tests the Acronis Cyber Protect Home Office app, a disaster recovery tool anyone can use to create a...more

Cybercriminals are creating fake cryptocurrency investment apps designed to defraud US investors and exploit investment firms, cautions the FBI. Image:...more

The goal is to help alleviate the estimated 700,000 vacancies in cybersecurity jobs in the U.S. Image: Maksym Yemelyanov/Adobe Stock...more

CSRB has released a report saying that the Log4j exploit is here to stay long-term, meaning businesses should be ready...more
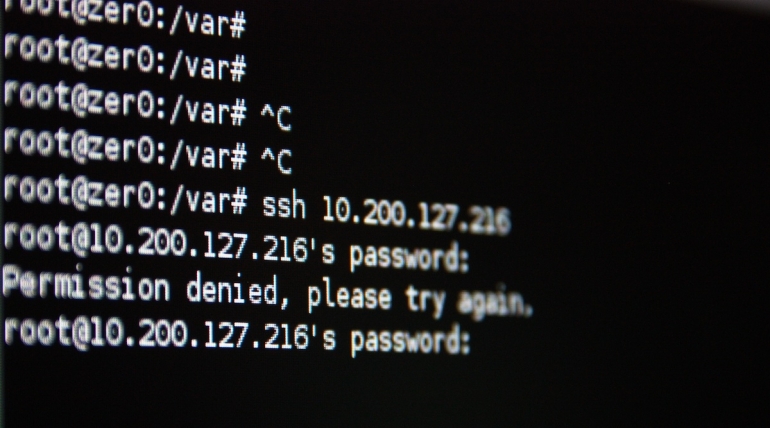
Image: pixeltrap/Adobe Stock SSH is a tool I use every single day to log into remote Linux servers and take...more

LinkedIn was exploited in almost half of the phishing attempts seen by Check Point Research during the second quarter of...more

Cyber fusion centers provide advanced security capabilities. Learn how your organization can strengthen its cyberdefense mechanism through a cyber fusion...more

Image: Adobe stock Must-read security coverage According to cybersecurity firm Trellix’s quarterly Threat Report: Summer 2022, released today, the line...more

Microsoft says a ransomware gang calling itself H0lyGh0st may be sponsored by the North Korean government as a way for...more

Image: jirsak/Adobe Stock With malicious actors more active than ever and criminal efforts growing ever-sophisticated, small and medium-sized businesses must...more