[video src="https://downfall.page/media/gds_spy.mp4" poster="https://downfall.page/media/gds_spy.mp4"] Learn technical details about this newly disclosed security vulnerability, as well as mitigation recommendations from the Google...more
[video src="https://downfall.page/media/gds_spy.mp4" poster="https://downfall.page/media/gds_spy.mp4"] Learn technical details about this newly disclosed security vulnerability, as well as mitigation recommendations from the Google...more
Among the surest method of jeopardizing employment within information technology is botching a server migration. Don’t let your career suffer...more
The process of installing or changing a data circuit involves internal personnel, building management, electricians and technicians from service providers....more
It’s important to maintain accurate infrastructure inventories to assist secure and effective network administration. A checklist, like the accompanying file...more

The computing space first announced in March is now open for general availability. The same type of hardware underpinned ChatGPT....more

YubiKey 5 Series multi-protocol hardware authentication device. (Image: Yubico) Derek Hanson, an expert on hardware-bound and syncable passkeys, works very...more

Newly discovered vulnerabilities in distributed control systems could allow attackers access to systems supporting industrial, energy, chemical and other operations....more

Skip to content TechRepublic Premium on July 13, 2023, 2:22 PM EDT Top Tech Conferences & Events to Add to...more

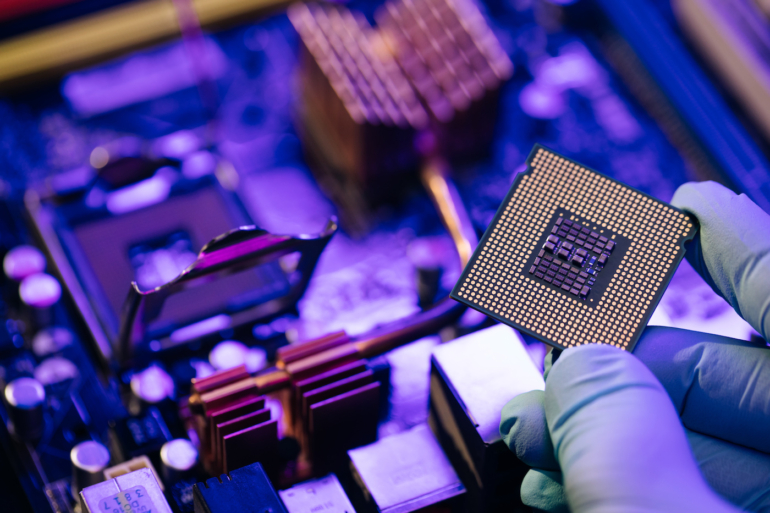
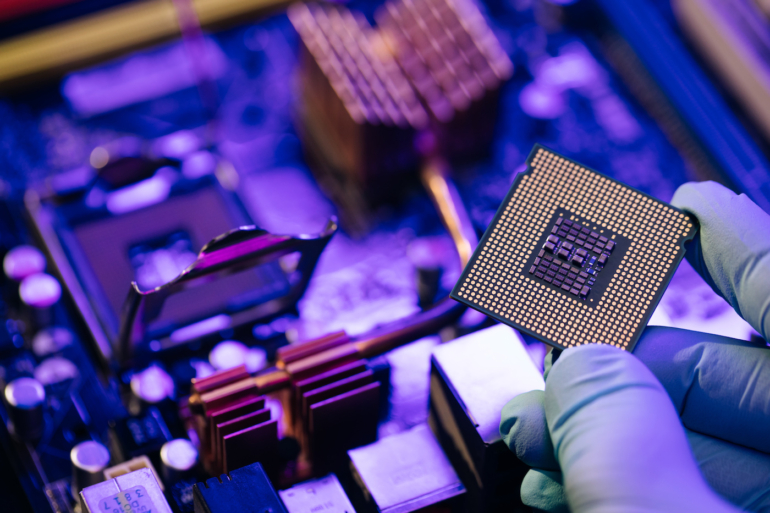
Learn about the benefits and use cases of quantum computing. Also, get details about quantum cryptography from an expert. Image:...more

Subscribe to the TechRepublic Premium Exclusives Newsletter Save time with the latest TechRepublic Premium downloads, including original research, customizable IT...more